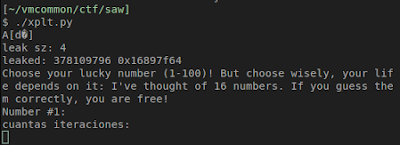
The remote service ask for a name, if you send more than 64 bytes, a memory leak happens.
The buffer next to the name's is the first random value used to init the srand()
If we get this value, and set our local srand([leaked] ^ [luckyNumber]) we will be able to predict the following randoms and win the game, but we have to see few details more ;)
The function used to read the input until the byte \n appears, but also up to 64 bytes, if we trigger this second condition there is not 0x00 and the print shows the random buffer :)
The nickname buffer:

The seed buffer:

So here it is clear, but let's see that the random values are computed with several gpu instructions which are decompiled incorrectly:


We tried to predict the random and aply the gpu divisions without luck :(

There was a missing detail in this predcitor, but there are always other creative ways to do the things.
We use the local software as a predictor, we inject the leaked seed on the local binary of the remote server and got a perfect syncronization, predicting the remote random values:

The process is a bit ugly becouse we combined automated process of leak exctraction and socket interactive mode, with the manual gdb macro.
The macro:
More information
- Hack And Tools
- Hack Tools Mac
- Hacker Tool Kit
- Pentest Automation Tools
- Easy Hack Tools
- Hacker Tools Windows
- Hacking Apps
- Pentest Tools Website
- Pentest Automation Tools
- Pentest Tools Nmap
- Hacking Tools Name
- Hacking Tools 2020
- Pentest Tools Free
- Hack Tools For Windows
- Nsa Hack Tools
- Pentest Tools Kali Linux
- Hacking Tools Software
- Pentest Tools Windows
- Underground Hacker Sites
- Hacking Tools For Games
- Hack Website Online Tool
- Hack Tools For Ubuntu
- Pentest Tools Linux



Tidak ada komentar:
Posting Komentar